Hackers Are Using Emojis to Blend In
For most people, emojis are a harmless method to avoid typing, but Flashpoint, a threat intelligence business, says that people in the online underworld are utilizing them in a bad way.
Flashpoint said in a corporate blog that the way adversaries talk to each other is changing as threat actors move away from formal, slow-moving communication platforms like Telegram and Discord. People frequently think of emojis as silly or non-technical, yet they have become an important element of that change.
Emojis are used in illegal forums, messaging applications, and closed groups not only to communicate feelings but also to show intent, sort activities, and sometimes even hide meaning from people who aren’t part of the group.
Flashpoint’s National Security Solutions Training Director Alanah Crocker said in a statement, “What we’re seeing in illegal communities is that emojis are being used as a consistent signaling layer alongside text.”
“They show things like access, monetization, targeting, and success in a way that is quick, easy to repeat, and often easier to scale across languages,” she said.
How Telegram and Discord Affect Threat Actors
Telegram and Discord have transformed the way threat actors talk to each other. Yagub Rahimov, CEO of Polygraf AI, an enterprise AI security company in Austin, Texas, said, “Telegram and Discord are giving threat actors encrypted, high-speed, short-lived channels with global reach and little moderation—something bad actors have never had.”
He told TechNewsWorld, “Communication has changed from structured dark web forums to fast-moving places where traditional monitoring doesn’t work.” “To many, it is data sovereignty, but for those nation states and other threat actors, it is freedom to damage.”
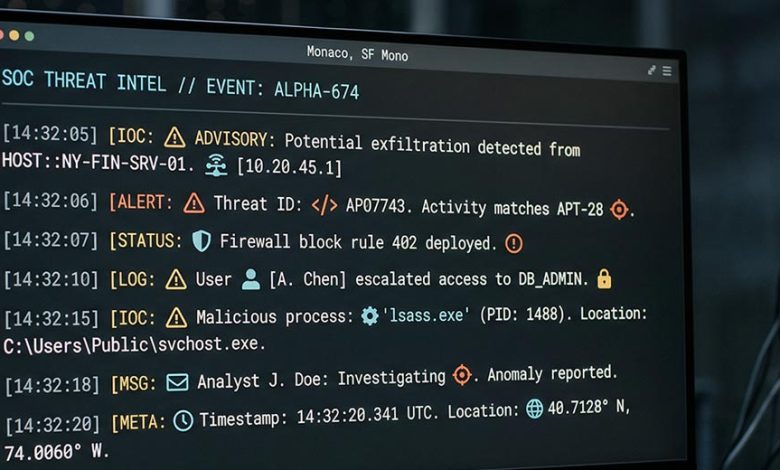
Ensar Seker, CISO of SOCRadar, a threat intelligence company in Newark, Del., said, “The move to platforms like Telegram and Discord has fundamentally changed how threat actors communicate because these environments are fast, semi-anonymous, and optimized for real-time coordination.”
He told TechNewsWorld, “In these channels, actors act more like agile teams than traditional forum users, and emojis fit in with that because they are light, language-neutral, and easy to recognize in groups around the world.” “This makes things easier in multilingual environments and lets threat actors work together quickly without having to use long-form text.”
How Emojis Can Help You Avoid Being Found
Karen Walsh, CEO of Allegro Solutions, a cybersecurity consulting company in West Hartford, Conn., said that threat actors mostly use Telegram because it offers the anonymity that Signal does, as well as the community that traditional forums used to provide.
“Threat actors are people, but they have bad intentions,” she told TechNewsWorld. “They use emojis to get their point across just like real users do.”
She went on to say that in online communities like TikTok, real individuals have gotten over keyword filtering for Palestine by using the watermelon emoji, which is the same hue as the Palestinian flag. At first, only a few individuals knew how to utilize this, but now it’s common in all programs.
“Threat actors are also using these pictures to get around keyword detection by making a visual shorthand that ‘insiders’ will understand,” she said. “As photos, the keyword filters won’t be able to find them, which gives threat actors another way to avoid being found. At the same time, they also make this social group feel like a community and give them an implicit sense of belonging.
Seker from SOCRadar said that traditional monitoring systems depend a lot on matching text, but changing or adding keywords with emojis can destroy existing algorithms. He said, “A phrase that would normally set off an alert can be made invisible or look harmless by simply replacing important words with symbols.”
He also said that utilizing pictures to draw attention to vital information is a good way to show how people absorb digital stuff. She said, “Most people skim information on the internet, and research shows that people read differently online than they do in print.” “The colors, shapes, and offset formatting of emojis make this even easier by making it easier to find the important information when skimming the content.”
Emojis are a sort of hidden communication that work like compressed operational shorthand. Polygraf’s Rahimov said, “Some of the most common keywords we see today are key emoji signaling stolen credentials, a money bag confirming payouts, and country flags designating targets.”
He said, “In the DISGOMOJI campaign, a Pakistan-linked APT group used emojis as real machine commands. A camera emoji took screenshots, a fire emoji stole files, and a skull emoji ended processes.” “This wasn’t slang. It was a simple procedure.
“Emojis are low-entropy encoding that hides in plain sight,” he went on. “A lot of the time, you wouldn’t even think it signifies anything. Regex-based filters don’t see anything that can be done when a threat actor replaces “stolen credit card” with a card emoji and multilingual slang. Tools made to look for string-based commands just stop working.
More and more, people are using emojis as short forms to show what they mean. Seker said, “An icon can show different stages of an operation, like targeting, exploitation, or monetization, without saying so directly.” “Some symbols may mean ‘access available,’ ‘credentials for sale,’ or ‘operation successful,’ which lets actors send sensitive messages in a shorter and less obvious way.”
He went on to say, “Threat actors also use emojis to sort activity streams in busy channels.” “In large Telegram groups, certain emoticons can act like tags to separate conversations about malware from those about data dumps, initial access offers, or financial scams. This makes a visual taxonomy that lets people easily sort through content that is relevant without having to use structured indexing.
Unclear Meaning
From a point of view of obfuscation, emojis make things unclear that automated systems find hard to understand. Seker said, “The same symbol can mean different things depending on the context, community, or even the specific threat actor group.” “This variability in context makes it harder for outsiders and detection systems to accurately figure out what the communications are trying to say.”
Mark Odom, a senior solutions engineer at Black Duck Software, an applications security business in Burlington, Mass., said, “This reminds me of the saying ‘A picture is worth a thousand words.'”
He informed TechNewsWorld that the same is true for an emoji. “Depending on the situation, an emoji can stand for a lot of things, such meaning, status, or intent. An emoji of a key could mean something harmless in one conversation, like someone forgetting their house key. In a different context, it may mean a list of qualifications.
He also said that a chain of emojis is something to think about. He inquired, “If a picture is worth a thousand words, how many words does a chain of pictures stand for?” “Even if law enforcement knew what a threat actor wanted to do, how would they be able to prove that intent without using simple language?” It makes it harder to find the talks and what you would need to verify the purpose.
He went on to say, “When it comes to using patterns to find threat actors, you can’t just use emojis to find these kinds of conversations.” In other circumstances, threat actors might include words along with emoticons, like “selling” before an emoji to show purpose. This could help, but it still doesn’t make any conclusions more reliable when you think about a lot of data.
Emoji Dialects
Rahimov, on the other hand, said that threat intelligence teams should consider emoji patterns as behavioral signatures and apply contextual techniques. He remarked, “In a nutshell, contextual behavior is the main weapon defenders have, because aliases can change but behaviors stay the same.”
Seker went on to say, “Patterns of use can actually become a signal on their own.” “Over time, certain groups create “emoji dialects” that can be followed. These patterns can be used by analysts for behavioral fingerprinting, linking activity across platforms, assigning campaigns, or finding actors who come back even when their usernames or infrastructure change.
He remarked, “The use of emojis shows how cybercrime ecosystems are becoming more professional.” “Like real businesses, these people are trying to make their operations more efficient, bigger, and more resilient.”
He said, “Emojis are not new.” “These are becoming part of the operational language of modern threat actors, and defenders need to treat them as such.”