Malware threats are growing faster in important infrastructure.

A report from the cybersecurity research site Comparitech, released on Wednesday, said that malware that affects industrial control systems (ICS) could disrupt important industries that support modern society.
Justin Schamotta, a researcher, said that threat actors are most interested in ICS devices that are connected to the internet, especially those that use old protocols like Modbus.
In his analysis, Schamotta found 179 ICS devices that were connected to the internet. He added, “We found one ICS device that was part of a national railway network.” “Railways employ ICS devices to help with everything from signaling to routing trains. Exposing these kinds of gadgets could pose a major risk to safety and operations.
He went on to say, “Two other devices, one in Asia and one in Europe, were part of the national power grid infrastructure of their countries.” “In the energy supply sector, ICS devices can be used to keep an eye on how much power is being used and manage how it is distributed.”
According to Schamotta, the US had the most exposed industrial control devices (57), followed by Sweden (22) and Turkey (19).
“Malware can break ICS systems and make them unusable, sometimes until a ransom is paid,” said Paul Bischoff, a Comparitech Consumer Privacy Advocate.
He told TechNewsWorld, “These systems are used in important infrastructure and manufacturing, so attacking them can have serious effects on the people and businesses that depend on them.” “Power plants, water treatment plants, hospitals, traffic control, and factories are just a few of the places that could be attacked.”
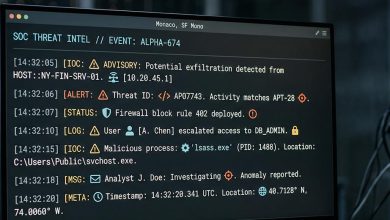
Attack Fallout Spreads Quickly “ICS malware crosses the cyber-physical divide and causes real-world kinetic damage,” said Shujaatali Badami, a quantum-IoT research engineer in Chicago.
He talked about the January 2024 attack in the Ukrainian city of Lviv, where malware dubbed FrostyGoop delivered Modbus commands to heating controls, stopping heat to almost 600 apartment buildings amid very cold weather. He told TechNewsWorld, “We are now tracking 26 OT threat groups and more than 11 ICS-specific malware families.” “This isn’t just a theory anymore.”
Michael Bell, CEO of Suzu Labs, an AI-powered cybersecurity company in Las Vegas, said, “ICS environments run the physical processes behind water treatment, power generation, oil and gas pipelines, and manufacturing lines.”
“When someone breaks into an IT network, you lose data,” he told TechNewsWorld. “When they get into an OT network, you can’t control the physical systems that keep people alive and the economy going.”
Attacks on ICS environments can also spread out a long way.
Floris Dankaart, the lead product manager for managed extended detection and response at the NCC Group, a global cybersecurity consultancy, said, “The industrial sector’s reliance on highly interconnected supply chains significantly amplifies the impact of attacks.”
He told TechNewsWorld that “a single successful compromise can cascade across suppliers, logistics providers, and downstream partners, magnifying disruption well beyond the initial target organization.” “This interconnectedness continues to make the industrial sector a good target for people who want to maximize their size and impact.”
ICS Vulnerabilities Rise
The Comparitech study also mentioned new research from Cyble Research & Intelligence Labs that showed the number of ICS vulnerability disclosures roughly increased from 2024 to 2025.
Shaila Rana, a senior member of the IEEE, a global technical professional organization, said, “ICS systems were originally designed to perform specific operational functions in isolated environments.”
“Security wasn’t a top priority because these systems were never meant to be accessible from the internet,” she told TechNewsWorld. “They were made for people and other machines to use.”
Rana said that over time, the push for remote monitoring and Industry 4.0 connectivity made that isolation go away. All of a sudden, these systems were exposed to a threat landscape they were never meant to handle. She remarked, “This convergence of IT and OT has greatly increased the attack surface.”
“While this is going on, the security research community has been paying more attention to OT environments. “More researchers looking means more vulnerabilities being found and disclosed,” she went on. “Legacy systems that are inherently insecure and more scrutiny are what is causing that sharp rise in disclosures.”
Joshua Marpet, a senior product security consultant at Columbus, Ohio-based Finite State, which automates security compliance and analysis for connected device manufacturers, said that part of the rise in vulnerability disclosures is the sheer number of new targets that are now connected.
He told TechNewsWorld that the same thing happened in the industrial world as it did with IoT devices like drones, Nest thermostats, and smart fridges. “Operational Technology and ICS/SCADA devices were linked so that they could be watched, managed, and controlled from afar. When devices are connected to the internet, bad people can view and attack them. So, just like some fridges were hacked, some factories were too.
Risks of Legacy Protocols
The Comparitech analysis said that the global market for industrial automation and control systems is presently worth $226.76 billion and is expected to increase to $504.38 billion by 2033. This means that the number of linked industrial devices is growing quickly.
This growth poses a major cybersecurity problem: every new device that connects to the network creates new potential attack surfaces that need to be safeguarded. ICS devices that are connected to the internet are easy targets if they don’t have the right protections like firewalls, VPNs, network segmentation, and secure authentication.
From an attacker’s point of view, devices that use protocols like Modbus, DNP3, or BACnet are especially easy to hack because they were made for closed networks and typically don’t have built-in authentication or encryption. If these gadgets were directly connected to the internet, attackers with no technical knowledge could take advantage of them. This is really worrying because some ICS devices are very important for economic activities and basic infrastructure.
Dale Hoak, CISO of RegScale, a compliance automation software company in McLean, Va., said that ICS security is not the same as traditional IT security. “You can’t just patch everything,” he told TechNewsWorld. “Downtime isn’t okay, and safety and availability are often more important than privacy.”
He went on to say, “If I had to put it simply, you don’t protect ICS by going after threats.” You keep it safe by always knowing what’s going on and keeping it under control.
Will Thomas, a senior threat intelligence advisor for Team Cymru, a threat intelligence company in Lake Mary, Florida, said that this is the “Era of Adoption” for ICS malware. This means that nation-state intelligence services are now using advanced digital weapons on a regular basis instead of just as experimental ideas.
He remarked, “Adversaries are using Operational Relay Box networks more and more to hide where they come from, and once they get inside a network, they use ‘living off the land’ tactics to avoid detection.” “Organizations must understand that legacy ICS devices should never be directly connected to the public internet in order to survive this very dangerous threat landscape.”
Risks of Longevity
Tim Mackey, head of software supply chain risk strategy at Black Duck Software, a Burlington, Mass.-based applications security company, said that one of the biggest problems with cybersecurity in critical infrastructure is that the devices last a long time.
He told TechNewsWorld, “Something that was designed and tested to the best practices available when it was released can easily become vulnerable to attacks using more sophisticated attacks later in its lifecycle.” “In fact, legacy best practices may not be able to stop current threats, or even worse, threats that could come up in the next few years.”
“Attackers know that critical infrastructure providers are measured by their up-time or service availability. Once a device is compromised, attackers know that they can plan a very targeted attack instead of just taking advantage of the situation,” he said.
Rosario Mastrogiacomo, chief strategy officer of Sphere Technology Solutions, a data governance software and services company in Hoboken, N.J., said, “One important point is that malware is only part of the story.”
He noted, “NIST has warned that OT loses its isolation and becomes more exposed as it adopts standard IT connectivity and remote access. CISA has also said that even simple methods can work against poorly secured OT environments.”
“For a lot of operators, the biggest gains still come from the basics: limiting internet exposure, making remote access more secure, separating OT from IT, knowing what assets are there, and getting ready for degraded or manual operations before something happens.”